The Learning Curve is officially live!
Vocareum's new podcast series exploring how AI is reshaping learning and work.
Build and deploy immersive cybersecurity labs—from ethical hacking with Kali Linux to network forensics—in a fully isolated, sandboxed environment. Provide your learners with hands-on access to real tools and vulnerable systems, with zero risk to your institution’s network. With Vocareum cyber labs, you can finally scale realistic cyber training without the complexity and danger of a physical lab.
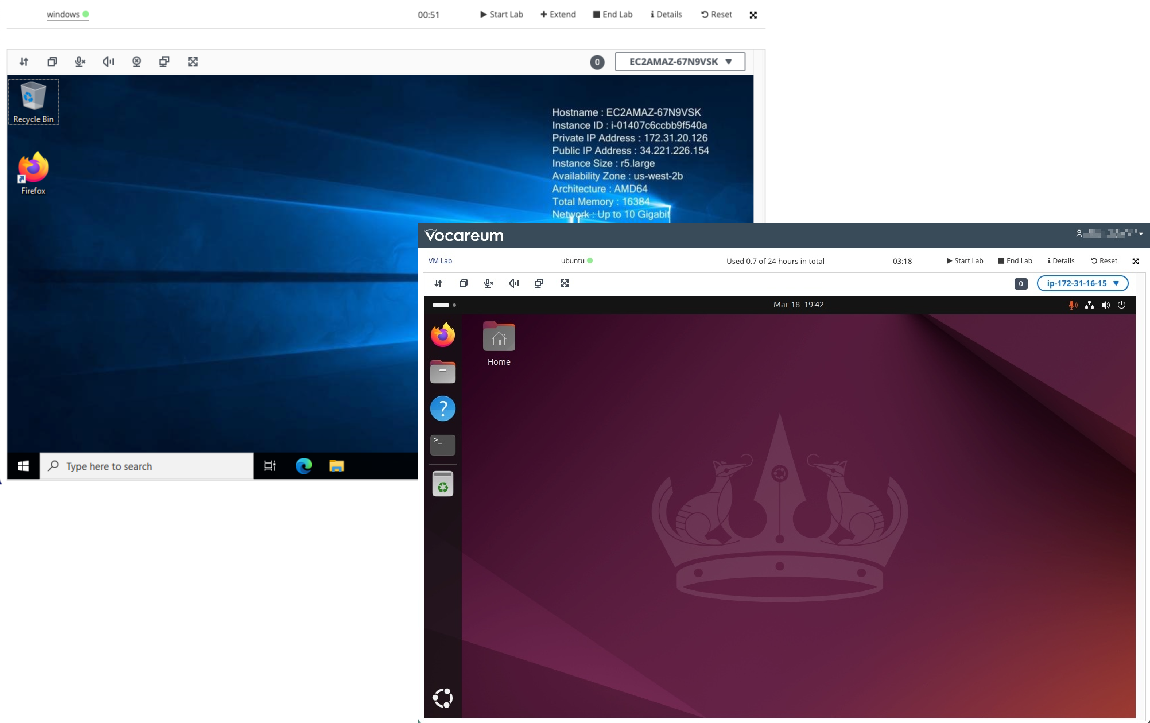
Create dynamic, multi-machine lab environments for any cybersecurity discipline.

Ethical Hacking & Penetration Testing
Deploy the complete offensive toolkit. Provide learners with Kali Linux environments to practice scanning, exploitation, and privilege escalation against a variety of pre-built or custom vulnerable target machines.

Threat Detection & Incident Response
Simulate a Security Operations Center (SOC). Let learners use tools like Wireshark, Suricata, and SIEMs to analyze network traffic, identify threats, and respond to incidents within a controlled network.

Investigate and Analyze Cyber Crimes
Create forensic investigation scenarios. Provide learners with disk images, memory dumps, and malware samples in a secure “detonation chamber” to perform analysis using tools like Autopsy without risk of infection.
Automated Assessment: Grade practical skills based on task completion.
LMS Integration: Launch labs and sync grades directly with your course.
Team-Based Exercises: Enable red team vs. blue team and other collaborative scenarios.
Centralized Management: Control all your cyber labs from a single interface.

Move beyond theory. Use our intuitive tools to construct complex network topologies, chain together multi-stage attack-and-defend scenarios, and automatically assess whether a student successfully achieved their objective. Bring your curriculum to life.

This is our core promise. Every cyber lab runs in a fully isolated, cloud-based sandbox, completely segregated from your campus network and from other students. We absorb the complexity and risk of running offensive tools and vulnerable software so you can teach with peace of mind.

Learners get access to the authentic, full-featured tools used by cybersecurity professionals. This isn’t a limited simulation. They will use the real Kali Linux, the real Wireshark, and the real Metasploit, allowing them to build practical, job-ready skills in a realistic environment.
Cover the full spectrum of your cyber curriculum, from introductory security concepts to advanced penetration testing capstone projects, all on a single, safe, and scalable platform.
Benefits:
Provide safe, equitable access to hands-on labs for all students.
Align your curriculum with NICE and CAE frameworks.
Assess practical, hands-on skills, not just theory.
Prepare learners for performance-based certification exams. Create realistic practice labs that mirror the challenges they will face to validate their hands-on competency.
Benefits:
Go beyond multiple-choice with hands-on skill validation.
Build learner confidence with realistic, high-stakes scenarios.
Deliver secure and consistent environments for every exam taker.
Continuously upskill your security analysts and penetration testers. Rapidly deploy new environments to train your team in the latest threats, vulnerabilities, and defensive tactics.
Benefits:
Keep your security team’s skills sharp and up-to-date.
Safely simulate attacks on models of your own infrastructure.
Run collaborative red team vs. blue team exercises to improve readiness.
We use multiple layers of network isolation in the cloud. Each student or team works in their own virtual private network that is completely firewalled off from the public internet (unless you explicitly allow it) and, most importantly, has no connection path back to your institution’s network. This creates a secure “bubble” for all lab activities.
Absolutely. This is a key use case. You can configure multi-user labs where students are assigned to different teams (e.g., Red and Blue) and given access to different machines within the same simulated network, allowing them to engage in real-time, collaborative exercises.
Our assessment engine is event-driven. You can create grading scripts that check for specific outcomes. For example, the script can check if a student successfully created a specific file on a target machine, accessed a database, or escalated their privileges to root. The grade is based on whether they successfully completed the objective, not just the commands they ran.
Book a demo to see the platform in action, or explore our case studies to discover how Vocareum can transform your training or educational program.

